 Are you looking for a way to manage Internet use on a single computer that’s being used by multiple people? To help you keep your browsing history and settings intact and keep unwanted users from accessing the web, Google has a free add-on available for Chrome created for just this very purpose.
Are you looking for a way to manage Internet use on a single computer that’s being used by multiple people? To help you keep your browsing history and settings intact and keep unwanted users from accessing the web, Google has a free add-on available for Chrome created for just this very purpose.
With this add-on, you gain the ability to essentially lock Chrome and only grant access to those you’ve given permission to use it. Although, this add-on is experimental, so be sure to keep potential issues in mind:
How to Install this Helpful Add-On for Google Chrome:
Open Chrome and enter chrome://flags in the search bar, now hit enter. From here, you will see a list of all the experimental add-ons available for Chrome. The one you want to track down is “Enable new profile management system.”
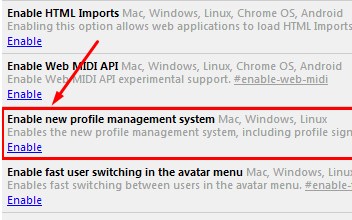
With the long list of add-ons before you, you’ve got the option to find the needed add-on a little quicker by using the CTRL+F (find) function.
Once you’ve located the add-on, click Enable. Next, close Chrome and open it again. You will now find the extension to be active. You can tell that the add-on is active because the sign-in screen will have a similar look to the sign-in screen used for Windows.
To login to your Chrome browser, select the Google account that you want to use, or enter the login credentials of an another account. Once logged in, you will be all set to browse the Internet like you normally would. Be sure to logout when you’re done. This will prevent other users from browsing Chrome with your Google account and messing with your settings.
Limitations of the Add-On
This add-on works great if you’re logged in and working with a single Google account. However, this add-on is designed to only work in conjunction with a single Google account, which means you will be unable to use a Google App, like Google Drive, under an account different than the one associated with the add-on. Therefore, this add-on isn’t ideal for users that routinely cycle through different Google accounts in single browsing sessions.
If you’ve installed the add-on and you don’t like how it limits your use of multiple Google accounts, then you can simply remove it by going to chrome://flags, finding the add-on, and clicking Disable.
This add-on is a great solution to keep unwanted people from using Chrome on your computer, but it’s doesn’t come close to protecting people from messing with other applications and settings on your PC, or deterring hackers. For a more comprehensive network security solution, call Total Tech Care at 866-348-2602.




