 Your business relies on a steady Internet connection to maintain operations. The inner workings of your cabling infrastructure are what ensure that you constantly have access to both online and offline networks for your organization. Most businesses utilize the services of major cable companies like Time Warner Cable and Comcast to facilitate this need, but some cities around the United States have access to another option: Google Fiber.
Your business relies on a steady Internet connection to maintain operations. The inner workings of your cabling infrastructure are what ensure that you constantly have access to both online and offline networks for your organization. Most businesses utilize the services of major cable companies like Time Warner Cable and Comcast to facilitate this need, but some cities around the United States have access to another option: Google Fiber.
Explaining Google Fiber
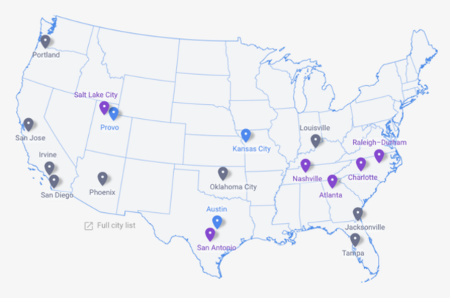
Originally, Google Fiber was only an experiment that was designed to deliver high-speed Internet and cable television to the Kansas City metropolitan area. Now, it’s a full-fledged Internet service provider, although its locations are limited to only a few cities within the United States.
As explained by CIO:
And optical fiber is the only choice for connectivity that exceed 1,000 Mbps, aka Gigabit Internet. Optical fiber provides higher bandwidths – download speeds 40 times faster and upload speeds more than 300 times faster than garden variety broadband – and spans much longer distances than electrical cabling. And some companies, such as Bell Labs, Cisco, and Comcast are claiming that their new "fiber optic" services (when eventually installed) will be 10 times faster than Google.
Does It Work?
The common consensus so far is that Google Fiber isn’t much different from other Internet service providers, and it’s a convenient service for those who want to keep their personal lives and businesses connected to the Internet. Unlike big names in the cable industry like Time Warner Cable and Comcast, however, Google Fiber isn’t associated with scandal and lackluster customer service, making it an attractive third-party choice. Businesses in areas where Google Fiber is available often cite that the service is cheap and convenient for their purposes, stating that they appreciate the fast Internet option.
In other cases, some users were dissatisfied with Google’s bundled service offerings, claiming that privacy is a major concern. Google’s systems scan users’ Internet activity in order to customize ads from Google and YouTube, which doesn’t sit well with some privacy advocates. These settings can be altered, but shouldn’t be touched without the knowledge of a trained professional technician.
Your business shouldn’t question whether or not you have reliable access to both your wired and wireless networks, especially for your applications and data stored in the cloud. If you lose access to both information and your software solutions, your business could be crushed by unexpected downtime costs. Therefore, what you require is reliability and scalability; the ability to shift your networking requirements in accordance with your business’s needs.
If you want to ensure reliability for both your wired and wireless technology, Total Tech Care’s skillful technicians can help your organization optimize its Internet deployment strategy. For more information, give us a call at 866-348-2602.




