Wait! If you haven’t read part one of our Facebook privacy blog yet, you may want to do that before reading this one. If you’re ready, we’ll be taking an in-depth look at your Facebook settings to make sure that your account and its data are as secure as possible. If we’re being honest, protecting this kind of data hasn’t seemed to be one of the platform’s strong suits - and user privacy has been the star of many lists of concern.
That’s why we wanted to make sure that you knew how to reclaim your personal data and make sure it is protected. We’ll start by protecting the information that you’ve shared.
To do this, you will want to access your Facebook account on a computer. This is going to be a lot to manage, and the mobile app would only be too much trouble to navigate.
Your Security and Privacy Options
From any page on Facebook, look for the menu, which will appear as a little downward-facing arrow. This should be at the top right-hand corner of the page. Click into Settings. This little arrow is your lifeline during this process, you can always find your way back to the beginning with that menu.
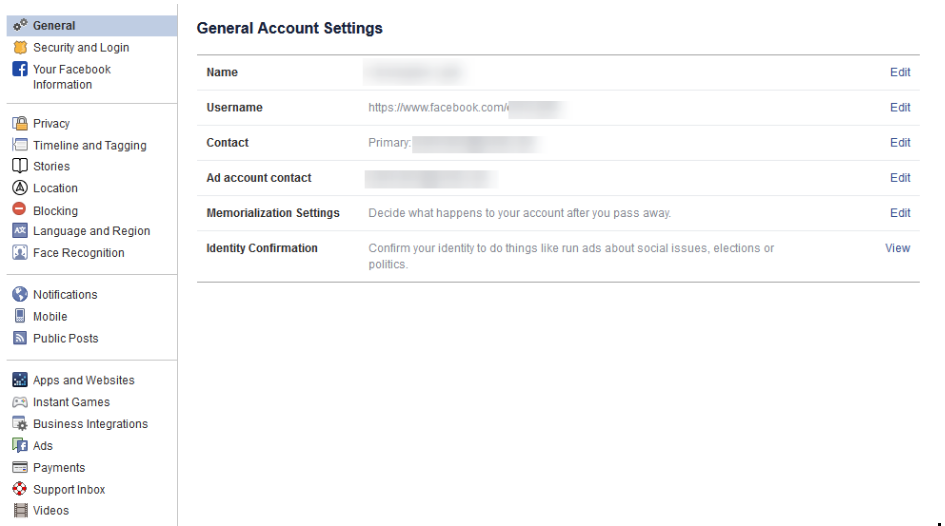
Verify the Accuracy of Your General Account Settings
Your first order of business should be to confirm that you still have access to all of the email accounts tied to your Facebook. If an account that you no longer have access to was used, account recovery becomes monumentally more difficult.
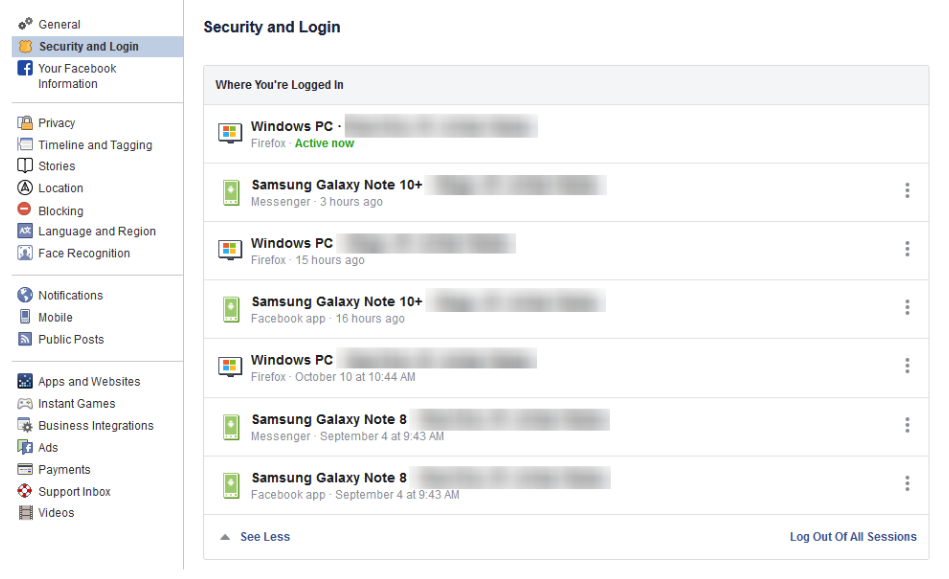
Find Out Where You’ve Used Facebook with Security and Login
On the right, you should see the Security and Login option. Click it, and Facebook will show you all of the devices where your account is logged in. Fair warning, this can be shocking - especially since it includes where and when you last used that device, and what browser you were using to do so. The longer a user has been engaged with Facebook, the more devices will likely show up here.
If one of these devices is one that you don’t recognize, you will want to change your password immediately - we’ll go over how in a moment. First, you will want to log out of Facebook on any device that you aren’t actively using. This can be done through the three-dot icon menus next to each device listed.
Change Your Password
While we’re on the topic, this is when you will want to make it a point to update your password. It will only take a minute and might just help keep your Facebook friends from being spammed and phished. You can do this using the process provided on the Security and Login page.
Remember, you should never use a password for more than one online account.
Using Two-Factor Authentication
After your password settings, you’ll see the option to set up two-factor authentication (2FA) to help protect your account. To set it up, select Use two-factor authentication and click edit, and Facebook will provide you with the instructions you need to follow. Click Get Started.
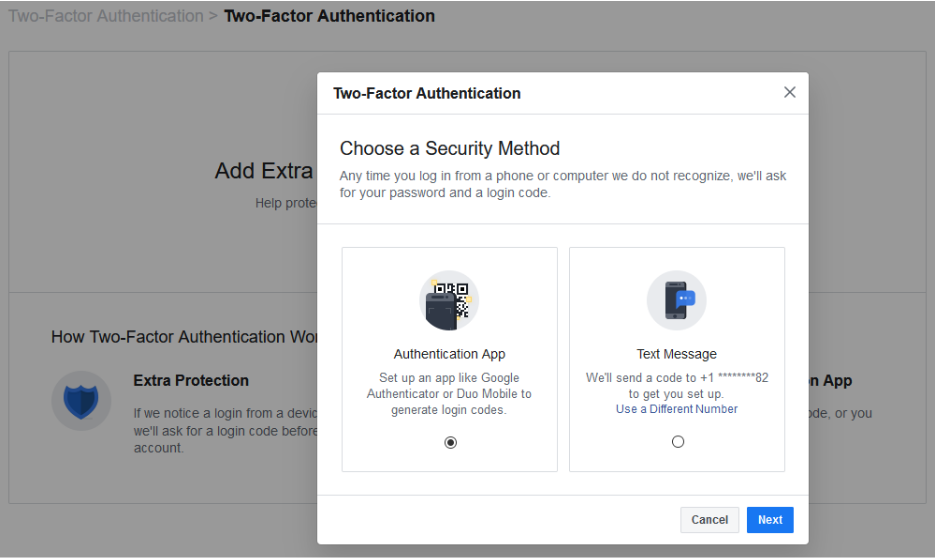
You have two options to select from as your Security Method, either using an authentication app, or to receive a text message with an additional code. Between the two, the application is the more secure option, although it does mean you need to have access to the mobile device whenever you want to check your Facebook.
Setting up the authentication app option is pretty simple. Open your application (which, if you have a Google account, might as well be Google Authenticator) and, on the computer, select the Authentication App option, as pictured, and click Next.
Facebook will display a QR code, which your authenticator app should allow you to scan when you add a new account to it. The app will then give you a six-digit number to provide to Facebook as a Confirmation Code. Simple.
If you decide to use the text message option, Facebook will simply send you a code that you have to provide upon login. It isn’t quite as secure as the app, but it will do. All you have to do to configure this is to confirm an initial code with Facebook, and you’ll be walked through the rest.
Add a Backup
Once you have two-factor authentication enabled, it only makes sense to add an additional means of 2FA as an emergency backup - in this case, whichever method you didn’t choose. Honestly, you might as well set up both, and make use of the Recovery Codes option, to boot.
Under the Add a Backup option on the Two-Factor settings page, there is also a Recovery Codes option. By clicking Setup, Facebook will provide a brief explanation, and the opportunity to Get Codes. Facebook currently gives you a list of 10 single-use 2FA codes. These are one-shot codes, but you can generate a new list whenever you want from the Two-Factor Settings page. Make sure you keep these codes in a safe place.
Setting Up Extra Security
Back on the Security and Login page, scroll down to find Setting Up Extra Security. This area lets you opt-in to alerts being sent via email or text, notification, or Facebook Messenger.
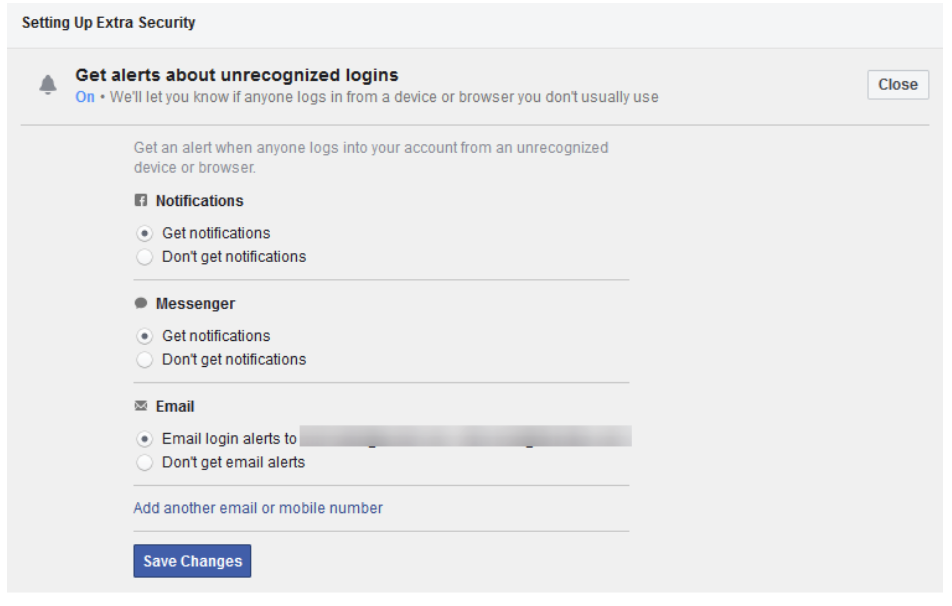
You can also Choose 3 to 5 Friends to Contact if you do find yourself locked out of your account. Make sure that these are people you truly trust.
Stay tuned for part three of this series, coming soon.





