 IT requires several factors in order to function properly. First of all, it can’t exist without information, and this information can’t exist without data. Technology is what creates data so that your company can take advantage of changes in the industry and business environment. It might seem like a lot to take in, but understanding the flow of data is necessary for a business owner. Otherwise, you won’t be able to take advantage of it to jumpstart sales and profitability.
IT requires several factors in order to function properly. First of all, it can’t exist without information, and this information can’t exist without data. Technology is what creates data so that your company can take advantage of changes in the industry and business environment. It might seem like a lot to take in, but understanding the flow of data is necessary for a business owner. Otherwise, you won’t be able to take advantage of it to jumpstart sales and profitability.
Granted, the difference between data and information is a bit difficult to understand in technical terms. Most businesses use these terms as if they are one and the same. While this is an acceptable practice in the industry, and it makes more sense to rationalize the two for marketing purposes, there’s still a significant difference between the two of them that should be understood by those who utilize technology.
In technical terms, data looks like a bunch of 1s and 0s in rapid succession. Naturally, this doesn’t make any sense to a human reading it; but to a machine that can interpret it, the data is able to take tangible form and compile the information we know and love that helps business owners make the best decisions for their organization.
This means that the process your business takes to collect data is exceedingly important. If the information isn’t accurate, there’s a chance that it can affect decisions when moving your business forward. The process of turning data into information is complicated, and there’s plenty of room for error. If even one part of this process is disrupted or weakened, the end result will reflect this.
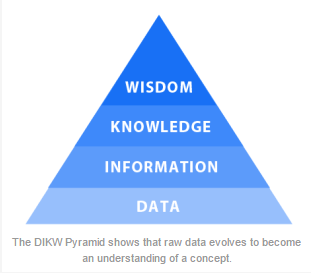
The DIKW Pyramid makes it much easier to analyze and understand the process through which data is transformed.
Business 2 Community provides us with a salad metaphor to describe the DIKW pyramid levels:
Data: I have one item. The data displays a 1, not a zero.
Information: It’s a tomato. Now, we understand the item and its characteristics.
Knowledge: A tomato is a fruit. We can identify patterns in the information and apply them to the item.
Wisdom: Tomato is never added to a fruit salad. There is an underlying, commonly understood principle that governs the item’s purpose.
B2C explains further by claiming that “bad data costs time and effort, gives false impressions, results in poor forecasts, and devalues everything else in the continuum.” Therefore, it’s necessary that the data your business collects allows for accurate and efficient analysis. Otherwise, your choices won’t be of the highest quality possible, and they could affect the functionality of your business in the future.
On the other side of the coin, if your technology is operating at maximum efficiency, and your communications are properly planned and managed, the chances of your data being affected by leaks or corruption is significantly reduced. As shown by the DIKW pyramid, data is the foundation for a business. Without it, you cannot hope to continue. Total Tech Care can help your business ensure that your data is safe and available when you need it with our Backup and Disaster Recovery solution. Give us a call at 866-348-2602 to learn more.




